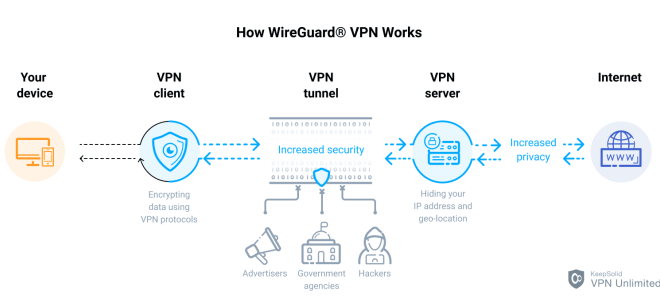
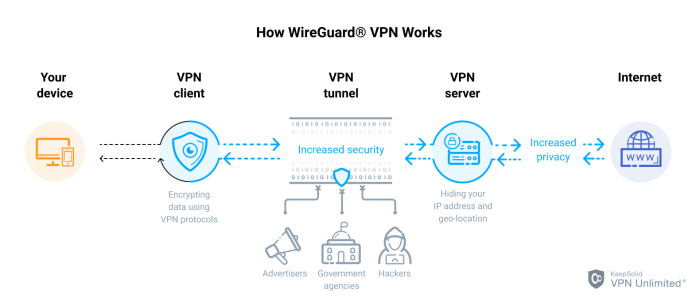
In the realm of virtual private networks (VPNs), choosing the right protocol is crucial for ensuring optimal security, speed, and privacy. Three of the most popular VPN protocols are IKEv2, OpenVPN, and WireGuard. Each protocol offers unique advantages and disadvantages, and understanding their differences is essential for making an informed decision.
This guide will provide a comprehensive comparison of IKEv2, OpenVPN, and WireGuard, covering their security protocols, performance and speed, privacy features, compatibility, mobile connectivity, multi-platform support, open source vs. proprietary nature, server configuration, client configuration, and troubleshooting.
Security Protocols
Security protocols play a pivotal role in establishing secure connections over VPNs. IKEv2, OpenVPN, and WireGuard employ different encryption algorithms, key exchange mechanisms, and security features, each contributing to their overall security posture.
IKEv2 utilizes AES-256 and SHA-256 for encryption and authentication, respectively. Its strong encryption algorithm ensures data confidentiality, while SHA-256 provides robust hashing for message integrity. OpenVPN offers a wider range of encryption algorithms, including AES-256, AES-128, and Blowfish, providing flexibility in choosing the desired level of security.
Key Exchange Mechanisms
The key exchange mechanism establishes a shared secret between the VPN client and server. IKEv2 uses the Internet Key Exchange version 2 (IKEv2) protocol, which provides mutual authentication and key exchange. OpenVPN employs the OpenSSL library, which supports various key exchange algorithms, including Diffie-Hellman and RSA.
WireGuard utilizes a unique key exchange mechanism called Curve25519, known for its speed and security.
Overall Security Strengths
IKEv2’s robust encryption algorithms and strong key exchange mechanism provide a high level of security. OpenVPN’s flexibility in encryption algorithms and support for additional security features, such as perfect forward secrecy, enhance its overall security. WireGuard’s modern key exchange mechanism and streamlined codebase contribute to its exceptional security and performance.
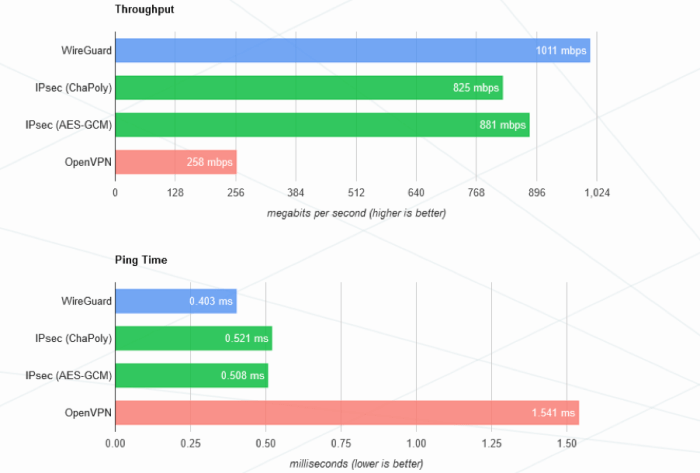
Performance and Speed
The performance and speed of a VPN protocol are crucial factors to consider when choosing the right one. Let’s delve into the connection speeds and latency of IKEv2, OpenVPN, and WireGuard.
The performance of a VPN protocol is influenced by various factors, including device capabilities, network conditions, and the encryption algorithms used.
Device Capabilities
- IKEv2 is known for its high performance on mobile devices due to its ability to quickly re-establish connections after a temporary loss of connectivity.
- OpenVPN offers good performance on a wide range of devices, including desktops, laptops, and mobile devices.
- WireGuard is designed for speed and efficiency, making it suitable for devices with limited processing power or for applications where low latency is critical.
Network Conditions
- IKEv2 and OpenVPN perform well on both wired and wireless networks.
- WireGuard is particularly efficient on high-speed networks, where it can provide faster speeds than IKEv2 and OpenVPN.
Encryption Algorithms
- The choice of encryption algorithm also affects performance.
- IKEv2 and OpenVPN support a variety of encryption algorithms, with AES-256 being the most secure but also the most resource-intensive.
- WireGuard uses ChaCha20 and Poly1305, which are designed to be fast and secure.
Performance Comparison
| Protocol | Connection Speed | Latency |
|---|---|---|
| IKEv2 | Good | Low |
| OpenVPN | Moderate | Moderate |
| WireGuard | Excellent | Very low |
Privacy Features
IKEv2, OpenVPN, and WireGuard prioritize user privacy by implementing robust encryption algorithms and employing advanced security protocols.
IKEv2 utilizes the Internet Key Exchange protocol, which establishes a secure channel for exchanging encryption keys. OpenVPN employs the OpenSSL library, renowned for its cryptographic strength. WireGuard, known for its simplicity and efficiency, utilizes modern cryptography algorithms, including ChaCha20 and Curve25519.
Logging Policies and Data Retention
IKEv2 and OpenVPN offer configurable logging options, allowing users to determine the level of data retention. WireGuard, however, does not maintain any logs by default, enhancing user privacy.
Comparison of Privacy Features
- Encryption Algorithms: All three protocols employ robust encryption algorithms to protect user data.
- Logging Policies: IKEv2 and OpenVPN offer customizable logging options, while WireGuard does not log any data.
- Data Retention: IKEv2 and OpenVPN allow users to configure data retention periods, while WireGuard does not store any data.
Compatibility and Device Support
When choosing a VPN protocol, compatibility with your devices and operating systems is crucial. Let’s explore the compatibility and device support for IKEv2, OpenVPN, and WireGuard.
IKEv2 offers wide compatibility with various platforms, including Windows, macOS, iOS, Android, and Linux. It’s natively supported by many devices, making setup and configuration relatively easy.
OpenVPN
OpenVPN boasts extensive device support, including Windows, macOS, iOS, Android, Linux, and even routers. However, it requires additional software or configuration for setup, which may not be as straightforward as IKEv2.
WireGuard
WireGuard is relatively new but gaining popularity due to its simplicity and performance. It’s primarily supported on Linux, macOS, and iOS. While Windows support is available, it requires more advanced technical knowledge for setup.
Mobile Connectivity
IKEv2, OpenVPN, and WireGuard all support mobile connectivity, but they differ in their handling of roaming and network switching.
Roaming
When a mobile device roams between different networks, IKEv2 and WireGuard can quickly re-establish the VPN connection. OpenVPN, on the other hand, may take longer to reconnect, as it requires a full handshake to establish a new connection.
Network Switching
When a mobile device switches between different types of networks (e.g., Wi-Fi to cellular), IKEv2 and WireGuard can seamlessly maintain the VPN connection. OpenVPN, however, may require a manual reconnect if the network change is significant.
Comparison
The following table compares the mobile connectivity features of IKEv2, OpenVPN, and WireGuard:
| Feature | IKEv2 | OpenVPN | WireGuard |
|---|---|---|---|
| Roaming | Fast reconnect | Slow reconnect | Fast reconnect |
| Network Switching | Seamless | May require manual reconnect | Seamless |
Multi-Platform Support
Multi-platform support is crucial for VPN protocols to cater to diverse user devices and operating systems. IKEv2, OpenVPN, and WireGuard offer varying levels of support across multiple platforms.
IKEv2 is widely supported across major operating systems, including Windows, macOS, iOS, Android, and Linux. Its native integration with these systems makes it easy to configure and use. However, some older or niche platforms may not have native IKEv2 support, requiring manual configuration or third-party apps.
OpenVPN is known for its versatility and cross-platform compatibility. It is supported on a wide range of devices and operating systems, including Windows, macOS, iOS, Android, Linux, and even routers. This makes it a suitable choice for users who need to connect to VPNs from various devices.
WireGuard is a relatively new protocol, but it is rapidly gaining popularity due to its simplicity and performance. It is supported on major operating systems like Windows, macOS, iOS, Android, and Linux. However, it may require manual configuration or third-party apps on some platforms.
Advantages and Disadvantages
IKEv2
- Wide native support across major platforms
- Automatic reconnection and roaming capabilities
- May not be supported on older or niche platforms
OpenVPN
- Excellent cross-platform compatibility
- Versatile and customizable
- Can be more complex to configure than IKEv2 or WireGuard
WireGuard
- Simple and efficient protocol
- Growing platform support
- May require manual configuration on some platforms
Multi-Platform Support Table
| Protocol | Windows | macOS | iOS | Android | Linux | Routers ||—|—|—|—|—|—|—|| IKEv2 | Native | Native | Native | Native | Native | Limited || OpenVPN | Native | Native | Native | Native | Native | Yes || WireGuard | Native | Native | Native | Native | Native | Limited |
Open Source vs. Proprietary
IKEv2, OpenVPN, and WireGuard differ in terms of their open source and proprietary nature. Open source software is freely available for anyone to inspect, modify, and distribute, while proprietary software is owned and controlled by a specific entity.
Open source software has the advantage of being transparent and customizable. Anyone can examine the code and verify its security and functionality. Additionally, open source software is often more flexible and can be adapted to specific needs. However, open source software may lack commercial support and may require more technical expertise to implement and maintain.
Proprietary software, on the other hand, is developed and controlled by a single entity. This can provide advantages such as professional support, regular updates, and compatibility with a wide range of devices. However, proprietary software can be more expensive and may not be as customizable as open source software.
IKEv2
- IKEv2 is an open source protocol developed by Microsoft and Cisco.
- It offers a good balance of security, performance, and compatibility.
- IKEv2 is supported by a wide range of devices and platforms.
OpenVPN
- OpenVPN is an open source protocol that is highly customizable and flexible.
- It offers strong security and supports a wide range of encryption algorithms.
- OpenVPN is supported by a large community of developers and users.
WireGuard
- WireGuard is a relatively new open source protocol that is designed to be simple, fast, and secure.
- It uses modern cryptography and is less resource-intensive than other protocols.
- WireGuard is still under development but has gained popularity due to its performance and security advantages.
Server Configuration
Setting up servers for IKEv2, OpenVPN, and WireGuard involves distinct configuration processes. Each protocol offers unique configuration options, and understanding these differences is crucial for effective server management.
IKEv2 Server Configuration
IKEv2 server configuration requires the creation of a certificate authority (CA), a server certificate, and a client certificate. The CA generates the server and client certificates, which are used for authentication and encryption. Additionally, the server must be configured with the appropriate IP addresses, ports, and security policies.
OpenVPN Server Configuration
OpenVPN server configuration involves generating a certificate authority (CA), a server certificate, and a client certificate. These certificates are used for authentication and encryption. The server must also be configured with the appropriate IP addresses, ports, and security policies. Additionally, OpenVPN allows for the use of custom encryption algorithms and ciphers, providing greater flexibility in security configurations.
WireGuard Server Configuration
WireGuard server configuration is relatively straightforward compared to IKEv2 and OpenVPN. It involves generating a public and private key pair for the server. These keys are used for authentication and encryption. The server must also be configured with the appropriate IP addresses, ports, and security policies.
WireGuard’s simplified configuration process makes it an attractive option for users seeking a more user-friendly setup.
Summary of Server Configuration Information
| Protocol | Certificate Authority | Server Certificate | Client Certificate | IP Addresses | Ports | Security Policies | Encryption Algorithms | Ciphers |
|---|---|---|---|---|---|---|---|---|
| IKEv2 | Required | Required | Required | Required | Required | Required | AES, 3DES | CBC, GCM |
| OpenVPN | Required | Required | Required | Required | Required | Required | AES, Blowfish, Camellia | CBC, GCM, EAX |
| WireGuard | Not Required | Not Required | Not Required | Required | Required | Required | ChaCha20, Poly1305 | N/A |
Client Configuration
Configuring clients for IKEv2, OpenVPN, and WireGuard involves setting up the necessary parameters to establish a secure connection to a remote server. Each protocol has its own unique configuration requirements, which vary depending on the platform and operating system being used.
IKEv2 Client Configuration
- Obtain the IKEv2 server address, username, password, and certificate (if required).
- Create a new VPN connection on the client device.
- Select IKEv2 as the VPN protocol.
- Enter the server address, username, and password.
- Configure the encryption settings (e.g., AES-256).
- Save the connection and connect.
OpenVPN Client Configuration
- Obtain the OpenVPN configuration file (.ovpn) from the VPN provider.
- Install an OpenVPN client on the client device.
- Import the .ovpn file into the client.
- Enter the username and password (if required).
- Connect to the VPN.
WireGuard Client Configuration
- Generate a public and private key pair for the client.
- Share the public key with the VPN provider.
- Obtain the server’s public key and IP address.
- Create a WireGuard configuration file with the necessary parameters (e.g., public keys, IP addresses, encryption settings).
- Load the configuration file into a WireGuard client.
- Connect to the VPN.
Troubleshooting
Troubleshooting VPN connections can be challenging, but understanding common issues and error messages can help resolve problems quickly.
IKEv2 Troubleshooting
- Authentication Failures: Verify credentials and ensure the server address and port are correct.
- Connection Timeouts: Check internet connectivity and firewall settings.
- DNS Issues: Update DNS settings on the device or use a custom DNS server.
OpenVPN Troubleshooting
- Server Connectivity: Ensure the VPN server is online and accessible.
- Firewall Rules: Check if the required ports are open in the firewall.
- Certificate Errors: Verify that the CA certificate and client certificate are installed correctly.
WireGuard Troubleshooting
- Peer Misconfiguration: Check that the public keys and IP addresses of both peers are correct.
- Firewall Issues: Ensure the firewall allows UDP traffic on port 51820.
- MTU Size: Adjust the MTU size on the client device if experiencing fragmentation issues.
| Error Message | Resolution |
|---|---|
| IKEv2: Authentication Failed | Check credentials or server configuration |
| OpenVPN: Connection Refused | Verify server connectivity or firewall rules |
| WireGuard: Invalid Endpoint | Check peer configuration or IP addresses |
Final Thoughts
Ultimately, the choice between IKEv2, OpenVPN, and WireGuard depends on your specific needs and preferences. If you prioritize security and speed, IKEv2 is an excellent option. For open-source enthusiasts and those seeking maximum privacy, OpenVPN is the preferred choice. And if you value simplicity, cross-platform compatibility, and cutting-edge performance, WireGuard is the clear winner.