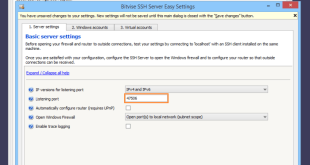
Secure Shell (SSH) is a powerful tool that provides secure remote access to servers. In this guide, we will explore the ins and outs of enabling SSH on Windows Server 2008, empowering you to harness its capabilities and enhance the security of your server infrastructure. With SSH, you can execute …
Read More »SSH Server
What Port Number Would You Open on Your Web Server SSH?
Securing your web server is crucial, and one essential aspect of that is managing SSH access. Choosing the right SSH port number is a critical decision that can impact the security and accessibility of your server. In this guide, we will delve into the considerations, best practices, and implications of …
Read More »The Remote SSH Server Rejected X11 Forwarding Request: A Comprehensive Guide to Troubleshooting and Resolution
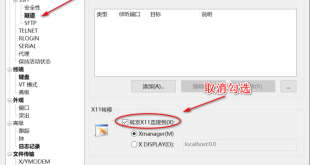
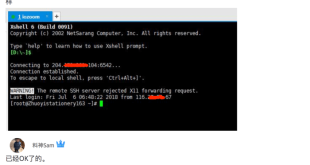
In the realm of remote connectivity, the Secure Shell (SSH) protocol reigns supreme, enabling secure and efficient access to distant systems. However, one common challenge that can arise is the rejection of X11 forwarding requests by the remote SSH server, hindering the display of graphical applications on the local machine. …
Read More »Troubleshooting “the Remote SSH Server Rejected X11 Forwarding Request”
X11 forwarding is a valuable tool for accessing graphical applications on remote servers, but it can sometimes be met with the frustrating error message: “the remote SSH server rejected X11 forwarding request.” This guide will delve into the causes of this issue and provide comprehensive solutions to help you establish …
Read More »Mastering SSH Tunneling Best Practices
SSH (Secure Shell) Tunneling is a powerful technique used to securely transmit data over a network. It encrypts the data during transmission, ensuring confidentiality and integrity. Mastering SSH Tunneling requires understanding its fundamentals and adopting best practices to maximize its benefits. Choosing the right SSH client Selecting the appropriate SSH …
Read More »Remote Access Made Easy with SSH Port Forwarding
Remote access to systems and networks has become an essential aspect of modern business operations. Whether you’re a system administrator, developer, or remote worker, being able to securely connect to your resources from anywhere in the world is crucial for productivity and efficiency. One of the most powerful tools for …
Read More »